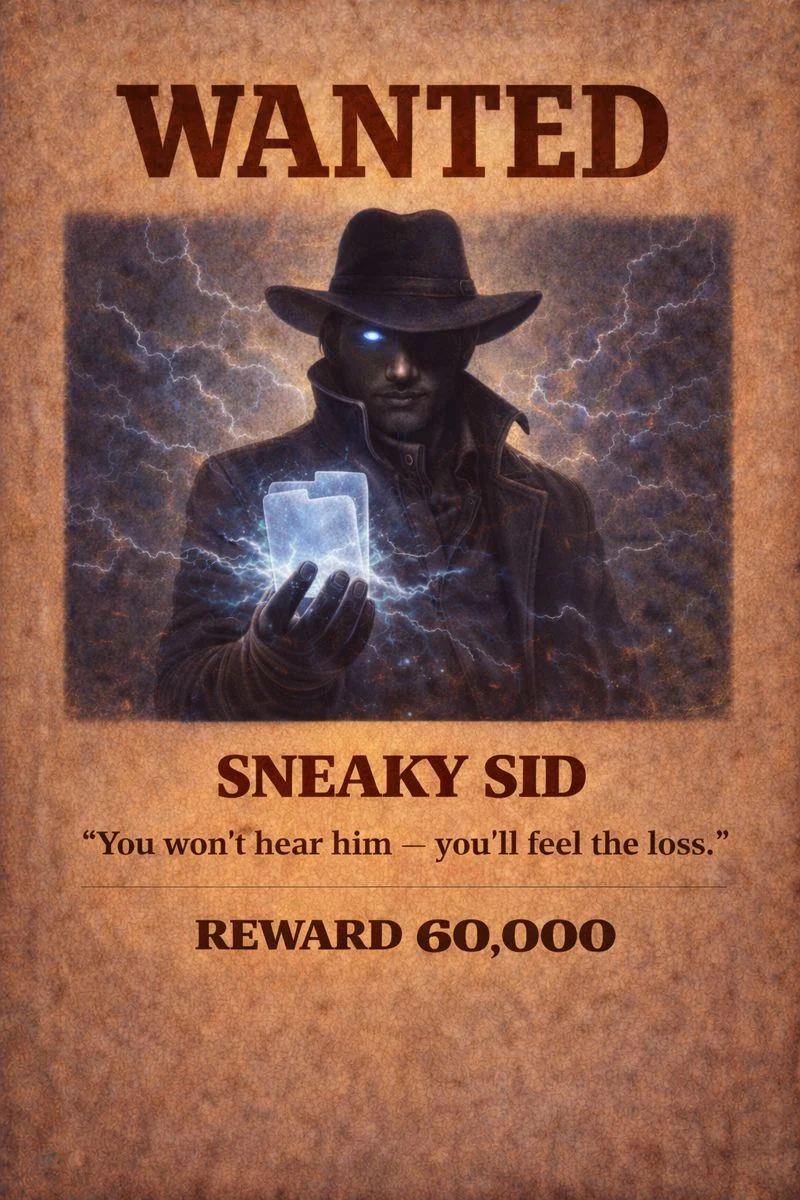
Unauthorised access occurs when attackers gain entry to systems, networks, or accounts without permission. Sid doesn’t break doors down – he waits for one left unlocked. Using stolen logins, misconfigured permissions, or weak security controls, he infiltrates systems and accesses data that was never meant to be seen or taken.

-Review access logs regularly and investigate unfamiliar logins
-Use strong, unique passwords and multi-factor authentication
-Limit admin privileges and apply the principle of least access
-Encrypt sensitive files and data stores
-Patch systems and close unused access points
