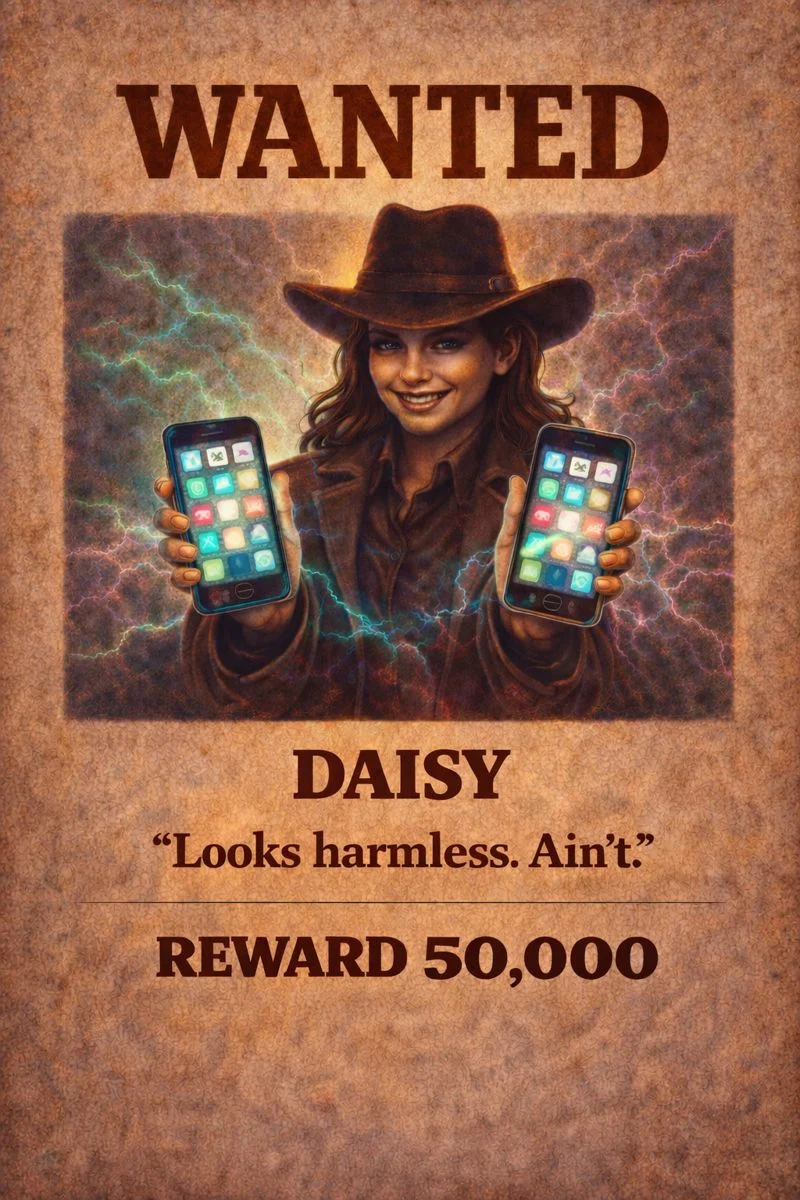
Malware & Exploits
The silent saboteurs of the digital frontier. Malware and exploit attacks use malicious code to infiltrate, corrupt, or control devices – often without the victim’s knowledge. Ransomware, spyware, trojans, and zero-day exploits are just a few of the tools these digital desperados deploy to seize your data.